 |
Audio Asylum Thread Printer Get a view of an entire thread on one page |
For Sale Ads |
 |
Audio Asylum Thread Printer Get a view of an entire thread on one page |
For Sale Ads |
96.3.196.74
This article regarding a Linux vulnerability is relevant to those running a Linux OS.
Follow Ups:
Again the Windows 10 'updated' itself. And naturally a bunch of my favorite programs were wiped out.
F*k Microsoft.
Windows 10 is like a phono cartridge..... Set up right, it works great; set up wrong, it will ruin your day.......



nt
By denying scientific principles, one may maintain any paradox.
Galileo Galilei
I don't get this - my computer says do you want windows 10 - click buttons - it installs - runs perfect. What's the problem? I had windows 7 on my laptop and windows 8 on my desktop - both upgraded to windows 10 zero problem.
Based on CVE count, Mac OS X and iOS are #1 and #2 for the largest number of known vulnerabilities, followed by Adobe products, followed by the big 3 browsers, then Windows & Linux in roughly equal measure. That doesn't speak to severity, but clearly Apple products are not nearly as safe as most Mac users assume.
Another thing to consider is that Microsoft is generally quickest to patch their vulnerabilities, followed by the big Linux distributions. Apple releases patches less frequently and takes longer to fix vulnerabilities. The commercial UNIX variants are the worst in that regard.
Many people mistakenly assume that if there aren't any obvious signs of infection, their computer is clean. Adware and ransomware are visible, but a lot of malware is not. Malware could be quietly keylogging or gathering data, or just sitting dormant waiting to be utilized by some hacker in a cyberattack.
I agree that many Mac users have a false sense of security but it is also true that there are fewer attacks on Mac systems vs PCs, for various reasons including market share. For attackers it's a numbers game.Based on CVE count, Mac OS X and iOS are #1 and #2 for the largest number of known vulnerabilities.....
FALSE
See the 2016 chart below.
Another thing to consider is that Microsoft is generally quickest to patch their vulnerabilities, followed by the big Linux distributions..... The commercial UNIX variants are the worst in that regard.
You have no evidence of this claim.
Which general purpose Linux or UNIX variant shows the fewest vulnerabilities? I didn't circle the "Real Time Extension" #50 in the list because it is not general purpose and it is not a full OS but an add-on (extension).

Edits: 10/21/16 10/21/16
Even if Mac OS X is not at the top so far this year, the 2016 data still reinforces my point, which is that Mac and Linux aren't inherently less vulnerable than Windows.
Since you're so quick to defend Apple, I'll point out that Mac OS X's rank in 2015 is not an aberration. Mac OS X and iOS were also #1 and #2 among operating systems in 2014. Mac OS X was also #1 in 2004, 2006, 2007, and 2008. And Mac OS is at the top of the all-time list. iOS is fifth on the all-time behind OS X, Linux kernel, Firefox, and Chrome. Apple also has three times more vulnerabilities per product than Microsoft on the all time list.
Regarding time to patch, that is just my anecdotal observation from work. Over the last 10 years, on the server side I've worked with Solaris, HP-UX, AIX, RHEL, CentOS, Windows Server, and s few instances of Debian, openSUSE, and Mac OS X Server. We patch and we run monthly vulnerability scans. My anecdotal experience has been that new Cat 1 vulnerabilities take the longest to get patched on the commercial UNIX platforms.
It seemed that your point was to disparage Apple with cherry picked data. Or perhaps you simply linked to an article that had old data w/o looking at the 2016 stats.
In any case, old data is not an indicator of current reality. One thing that wasn't mentioned and not available on the CVE site is that Apple has the highest adoption rate among their user base for updating to new OS and application releases.... which translates to fewer open vulnerabilities. This is true with Android vs iOS new release adoption as well as Windows vs Mac OS X.
My observation based on personal experience, along with what I hear from several co-workers, is that we have had significantly fewer virus and malware issues since switching from Windows to Mac OS X. The sample size is small but our group of about 35 individuals all switched from Windows to Mac at the same time about 7 years ago. We were all issued company supplied Macs.

I've been using Mac OS X since 2001 and I'm partial to Mac laptops. They kind of lose me with their desktop offerings but that's beside the point.
I have also noticed that on average, fewer Mac users report problems with malware compared to Windows. But I've also noticed that a lot of Mac users have a false sense of security i.e. I bought a Mac so I don't need to worry about malware. Same for Linux users.
I guess my main point is that just because people aren't reporting problems doesn't mean they're not infected. Like when Flashback made the rounds a few years ago, most of the people who had it on the Mac didn't notice it was there. That kind of malware, which stays hidden and harvests data you type into your browser (userids, passwords, cc info, etc.) is arguably more dangerous than the adware that people do notice.
But as you admit yourself, that doesn't speak to severity, and some (many?) of those vulnerabilities which show up in the "counts" are theoretical in the sense that they've been proven in the lab, but have never shown up "in the wild".
I do agree with your last paragraph, even though I've never used anti-virus software on any of my Macs since the turn of the century. And if the Russians are somehow using my Mac to help gather data on Hillary's illegal machinations, then I'm proud to be of assistance - not that I'm for Trump by any means! A pox on both of them! ;-)
Todd,
Thanks, but FYI, these are ongoing. :) If you are on the mailing lists, you'll see something like this about every 3-6 months from kernel issues to OpenSSH, etc.
That's why it's important to apply security patches quickly.
Also, some issues don't really matter to the home user unless you have server that faces the Internet, such as a web server. You can't suffer from a SQL injection hack without a database running and a port open to the world. :-)
By all means, apply security patches early, but don't flip out. :)
Best,
Erik
Ah, okay. FWIW, I don't even run Linux, but it seemed something that the rest of the forum may have interest in, especially in view of the discussion below. It seems preferable to pass it on and have it be common knowledge, as you've pointed out. Or maybe not...guess I'll find out, eh? ;-)
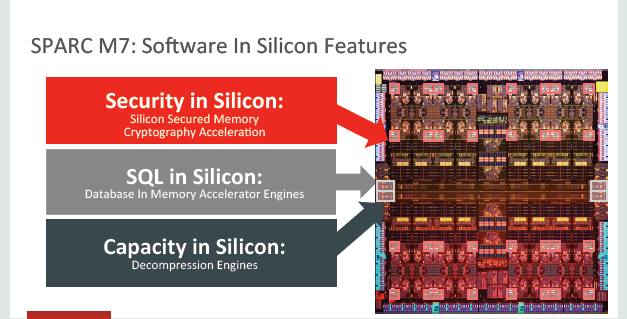
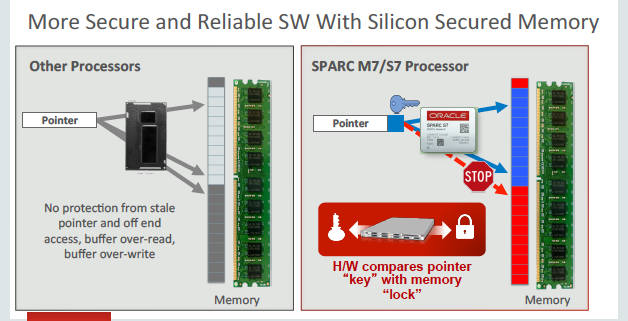
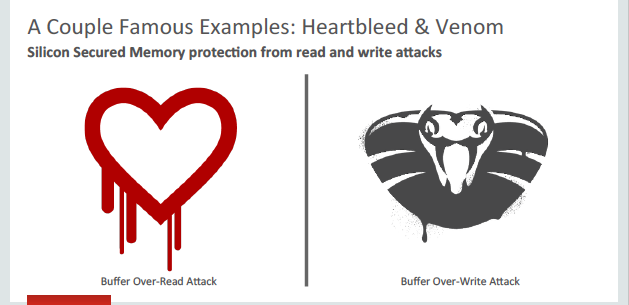
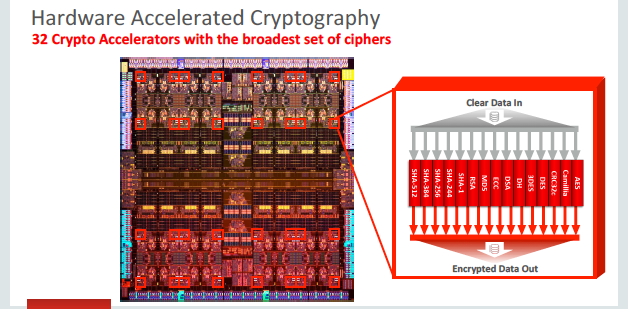
There ARE UNIX based systems that will never experience this sort of problem. If you read more detail about the Linux security vulnerability (linked below), it is memory related. The solution is to prevent it from happening at all, rather than having antivirus software detect it as the article alludes to.
Not Linux, not x86:
For a music server? Nah. For banking and national security? Of course!

Post a Followup:
| FAQ |
Post a Message! |
Forgot Password? |
|
||||||||||||||
|
||||||||||||||
This post is made possible by the generous support of people like you and our sponsors: